April 9, 2026
.png?width=400&height=150&name=My%20project-1%20(1).png) by Tanuja Bahirat / April 9, 2026
by Tanuja Bahirat / April 9, 2026

If there’s one thing working cross-functionally has taught me, it’s that secure access isn’t just a security priority; it’s a growth enabler. Slow logins and brittle VPNs kill momentum; over-permissive access invites incidents.
The difference often comes down to the platform behind the scenes. The best zero trust networking software doesn’t just gate access; it aligns identity, device posture, and app context so users get where they need to go, quickly and safely. To see what truly stands out, I compared leading ZTNA solutions across policy depth, IdP/EDR integrations, deployment speed, and day-two operations.
If you're searching for the best zero trust networking software for 2026, here are my top picks. Whether you need a zero trust solution for securing office network, centralizing identity across a distributed workforce, or segmenting sensitive apps before rolling out adaptive authentication, these platforms stood out for flexibility, scalability, and real-world usability.
The lineup spans Zscaler Private Access for VPN-free app connectivity, Cisco Duo for adaptive MFA, Palo Alto Networks IoT/OT Security for device-level visibility, Okta for identity-driven access, and FortiClient for unified endpoint protection.
These best zero trust networking software are top-rated in their category, according to the latest G2 Spring 2026 Grid Reports. Contact the sales team for accurate pricing details.
Zero trust networking platforms enforce “never trust, always verify” for application access across hybrid and remote work. Instead of routing users through network-level VPNs, they continuously validate identity, device posture, and context, then grant precise, app-level access that limits lateral movement.
The business case is straightforward: breaches are costly and common. IBM states the global average cost of a data breach is about $4.4 million, reflecting a 9% drop from the previous year, a decline largely attributed to organizations detecting and containing incidents more quickly.
With that in mind, I prioritized platforms that pair clean policy models and strong integrations (IdP/EDR/MDM) with reliable clients and clear visibility. Based on reviews, demos, and hands-on tests, these are the five I’d pick if you’re serious about operationalizing zero trust.
I started with G2’s Grid Report, which ranks tools based on real user reviews and market presence, to move past surface-level comparisons. The Grid gave me a solid foundation that highlighted both established leaders and innovative challengers in the zero trust networking category.
I then used AI-assisted analysis to dig into hundreds of verified G2 reviews. I paid close attention to patterns around policy reliability and enforcement, ease of integration with identity providers (IdPs), EDR/MDM, and SIEM tools, depth of device posture checks and app discovery, and scalability across users, apps, and locations. This helped me see what security, IT, and networking teams actually value most, and where zero trust platforms sometimes fall short.
To bring the data into a real-world context, I also connected with fellow G2’ers who work with zero trust access in security operations, IT, and network engineering. Their experiences validated the themes I found in the reviews and shed light on implementation speed, setup experience, and the day-to-day impact these platforms have on both user productivity and overall security posture.
All product screenshots featured in this article come from official vendor G2 pages and publicly available materials.
I considered the following factors when evaluating the best zero trust networking software.
The list below contains genuine user reviews from the Zero Trust Networking category. To be included in this category, a solution must:
*This data was pulled from G2 in 2026. Some reviews may have been edited for clarity.
Among zero trust options for private app access, Zscaler Private Access (ZPA) shows up repeatedly in G2 reviews for doing what most teams actually need: broker fast, policy-driven, user-to-app connectivity. If your goal is to retire brittle VPN tunnels, reduce lateral movement, and give users a consistent way to reach internal web, client-server, and cloud apps from anywhere, ZPA is built for that job.
What G2 users call out most often is how secure access feels routine once ZPA is in place. In fact, 92% of G2 users rate the application security highly. The combination of identity-aware policies and least-privilege access means you can tighten control while keeping the experience simple, people launch the apps they need, and nothing else.
Reviewers also highlight the global footprint and scaling behavior: standing up access for distributed teams and contractors is straightforward, and policies can expand with new apps and regions without major re-architecture. In day-to-day terms, that translates into fewer “can’t reach the app” tickets and less time spent micromanaging network paths.
The time-to-value and setup practicality often come up as a positive in G2 reviews. Many admins describe the initial rollout as clear. There are publishing apps, mapping policies to identity groups, and onboarding users with minimal to no friction. ZPA’s ecosystem fit also gets consistent praise: integrations with major IdPs for SSO/MFA, plus hooks into EDR/MDM and SIEM/ticketing, help teams keep identity, device posture, and audit signals in one loop.
Let’s talk about performance. Users note snappy access and low perceived latency compared to legacy VPN, especially for web apps, with fewer slowdowns due to tunnel congestion. Coupled with client and connector architecture that abstracts away network complexity, many teams say ZPA makes remote access feel invisible: users click, the service verifies identity and device posture, and the session just works. For IT, that “feels like SaaS” quality is a big part of why ZPA replaces tactical VPNs rather than sitting next to them.

A recurring theme I noticed in recent G2 reviews is the granular control ZPA offers at the user and application level. Admins appreciate the ability to define precise whitelisting and blacklisting rules that reflect almost instantly, along with logging and activity review features that make it easy to track who accessed what and when. That level of visibility doesn't just improve day-to-day security oversight; it also simplifies compliance reporting and audit preparation, which G2 users say saves significant admin time. In fact, 92% of G2 users rate its security analytics highly, and the platform holds a 91% rating for network segmentation capabilities.
Several G2 reviewers say the agent/client needs hands-on tuning in the first couple of weeks, tightening rules, mapping app segments, and refining device-posture checks. This is best for teams that want granular, policy-driven control rather than pure plug-and-play. Once policies settle, the payoff is consistent: VPN tickets drop, access becomes predictable and fast, and security teams gain clear visibility into who accessed what, from which device, under which conditions.
G2 budget owners note that pricing scales with footprint (regions + app-dense estates), so upfront growth modeling helps avoid surprises. This model suits organizations planning global coverage and broad integrations, and teams that model growth early say spend becomes predictable, consolidation offsets costs, and the operational gains hold: less lateral movement, fewer brittle tunnels, and a user experience where people don't fight the tools to get their work done.
A modest upfront investment in client/policy tuning and scale modeling yields what teams value most: fast, predictable private-app access, fewer VPN tickets, and clear end-to-end visibility. In practice, ZPA scales with your business and largely gets out of the way, tightening control without adding friction.
“I really like that Zscaler Private Access is automated. It's turned on by default, which is a very interesting feature because when I'm using different software, I usually have to connect and disconnect, which can be a hassle. But with Zscaler Private Access, it's automatically opened, and it never turns off for any reason. So it's always turned on automatically, which is great. I don't have to do anything.”
- Zscaler Private Access review, Mario M.
“In whitelisting, sometimes it requires whitelisting another sub link to work, which I think needs to be improved. Applying sub-categories or suggestions when whitelisting URLs to make things work would be helpful.”
- Zscaler Private Access review, Mohamed G.
Zero trust starts with identity. Explore the top tools enabling this shift in our guide to identity and access management software.
If there's one feature that defines the Cisco Duo experience in G2 reviews, it's the push-based MFA.
The tap-to-approve push notification model is the single most mentioned feature across recent feedback; users describe a login flow where security adds seconds, not friction. If your goal is to layer strong identity verification on top of every access point without slowing people down, Duo is built for that balance.
One thing I kept seeing in reviewer feedback is how quickly teams get Duo up and running. Both admins and end users describe a setup process that requires minimal IT overhead, no lengthy deployment cycles, and no complicated configurations for the average user. In fact, 95% of G2 users rate the ease of admin highly, and the platform reports a 70% average user adoption rate with a 7-month payback period. That combination of fast deployment and rapid adoption means teams start seeing security returns quickly.
Duo's integration depth came through as a consistent theme in G2 reviews. The platform connects cleanly with VPNs, SSO platforms, cloud applications like Microsoft 365, directory services, and legacy systems. Reviewers describe plugging Duo into their existing stack without rebuilding workflows, and that ecosystem fit means identity verification stays centralized rather than scattered across disconnected tools.
A pattern I noticed across recent G2 feedback is how Duo's zero trust model checks both user identity and device posture before granting access. Reviewers highlight that the platform assesses device health alongside authentication, so access decisions factor in real-time risk signals rather than relying on credentials alone. With 90% of G2 users rating adaptive access control highly, teams get a meaningful layer of protection that adjusts to context without requiring manual intervention.
Several users specifically describe using Apple Watch to approve authentication prompts in situations where pulling out a phone isn't practical, during meetings, in labs, or while commuting. That cross-device convenience removes a common pain point with traditional MFA and helps explain why adoption rates stay high even in non-technical teams.
From an operator perspective, G2 reviewers call out the admin dashboard as a practical strength. The console provides clear visibility into authentication events, user activity, and policy status, helping security teams monitor what's happening without sifting through raw logs. Reviewers note that this clarity makes compliance reporting easier and gives IT leads confidence that access controls are working as intended.
Duo's phone-based authentication model is a strength for speed and convenience, but G2 reviewers note that access can be disrupted if a user's device is lost, dead, or out of connectivity range. That said, the platform does offer fallback options like passcodes and backup methods, teams that configure these recovery paths during initial rollout report smooth handling of edge cases, keeping security tight without locking people out.
The platform's access policies cover most environments well, though some G2 reviewers in highly regulated industries or complex hybrid setups mention wanting more granular customization for location-specific or role-specific rules. Duo continues to expand its policy engine, and teams that invest time in tailoring MFA prompts and session settings to their risk model report that the platform meets their enforcement needs while keeping the end-user experience clean.
From what I've seen, Cisco Duo is a strong fit for teams that want to raise their identity verification bar quickly, without burdening end users or overloading IT.
"I like that Cisco Duo allows me to verify my identity on different platforms and devices I have, which makes it convenient to do that on my personal device. It makes it valuable because I can access the sensitive information I need without having to go through other channels or apps. Plus, the initial setup was extremely easy."
- Cisco Duo review, Kenneth T.
"Duo provides basic logs and reports, but advanced analytics or security insights are limited, so companies sometimes export the data to external SIEM tools for deeper analysis."
- Cisco Duo review, Kamalesh Kumar S.
Want to strengthen your zero trust stack? Learn how multi-factor authentication adds an extra layer of protection without slowing users down.
What stood out in my evaluation is the unified IT/OT lens. Palo Alto Networks IoT/OT Security repeatedly shows up in G2 reviews for doing the essential groundwork well: discovering and classifying devices, surfacing behavioral anomalies, and giving teams a unified, searchable view of what's actually connected. If your goal is to move from guesswork to a defensible, real-time asset picture, this is the kind of foundation you need.
Reviewers consistently highlight how the product brings operational technology into the same line of sight as traditional IT, making it easier to see PLCs, HMIs, cameras, sensors, and printers without stitching together multiple tools. That consolidated view isn't just cosmetic; G2 users say it shortens triage because ownership is clearer and suspicious behavior is easier to spot in context.
Discovery and classification accuracy also came through strongly in G2 reviews. Reliable fingerprinting of IoT/OT assets and faster inventory buildouts translate to fewer blind spots, quicker identification of unknowns, and more confidence when you attach policy. Paired with behavioral and anomaly detection, teams report actionable alerts that improve with tuning less noise, more signal, so responders aren’t sifting through endless low-value events.
Integration depth is another repeated theme in G2 feedback. The product plays well with identity (IdP), endpoint (EDR/MDM), SIEM, ticketing, and NGFW/Prisma workflows. That matters when you want detection to lead to enforcement or when you need incidents to show up where your team already lives; reviewers frequently mention how these connections reduce swivel-chairing, tighten response loops, and make audit narratives clearer.

G2 users also call out dashboards and reporting. Topology views, risk summaries, and device-level drill-downs make complex environments legible and defensible: you can show what's talking to what, why it's risky, and what actions you took. In fact, 90% of G2 users rate its security analytics capabilities highly. For many teams, that "show your work" moment is what turns a good pilot into an operational win.
A theme that came through clearly in recent G2 reviews is the platform's machine-learning-driven approach to risk assessment. Reviewers describe how the AI automatically profiles device behavior, assigns risk scores, and surfaces anomalies with precision, reducing the manual effort that typically goes into identifying which devices pose the highest threat. With 90% of G2 users rating user monitoring capabilities highly, the data backs what reviewers say: this intelligent profiling doesn't just flag issues; it learns over time, so the signal-to-noise ratio improves the longer the platform runs. That adaptive quality makes it particularly valuable in environments with thousands of diverse devices where manual monitoring simply can't scale.
Another capability that G2 reviewers highlight repeatedly is the platform's ability to discover and classify devices without requiring agents or additional hardware sensors. For IoT and OT environments where installing software on each device isn't feasible, think legacy PLCs, medical equipment, cameras, or building-automation systems, that agentless approach eliminates a major deployment barrier.
G2 reviewers appreciate the depth and unified view, but several note the console can feel dense at first, especially in multi-site rollouts where roles, groups, and workflows need planning. That said, the same feedback consistently points to a quick settlement once onboarding is complete: alert noise drops, ownership becomes clearer, and investigations move faster as OT signals feed existing SIEM/SOAR pipelines, making the initial investment in console orientation well worth the effort.
Because the platform consolidates meaningful capabilities, some G2 users describe pricing and licensing as being on the higher side and say they'd like clearer guardrails as device counts grow. However, teams that plan for future scale and forecast usage early on report that costs become easier to predict, and that consolidation ultimately offsets spend by reducing support tickets, closing visibility gaps, and strengthening audit readiness, delivering lasting ROI that justifies the upfront modeling.
Overall, rated a 4.3/5 on G2, reviewers appreciate that it can introduce it alongside existing network and security architectures and then elevate controls as visibility improves. It’s a practical path to reducing risk without pausing the business. Repeated G2 themes point to a platform that delivers a trustworthy inventory, fewer blind spots, and faster, better-informed decisions when something starts behaving out of band.
“What really stands out about Palo Alto Networks IoT/OT Security is how effortlessly it secures every connected device across the network. It automatically discovers all IoT and OT devices, even those that are usually missed, and gives a complete view of what’s happening. The best part is that it detects and blocks threats in real time, keeping everything safe with very little manual effort.”
- Palo Alto Networks IoT/OT Security review, Ritika G.
“There isn’t much to dislike. The only minor challenge is the initial learning curve; it takes a bit of time to fully explore all the analytics and policy options. But once properly configured, it runs smoothly and requires minimal manual intervention. The insights it delivers make the setup effort absolutely worth it.”
- Palo Alto Networks IoT/OT Security review, Pawan M.
Explore the best Network Access Control software on G2. Compare top NAC tools built to enforce zero trust policies and secure every device on your network.
The first thing that became clear as I went through Okta's G2 reviews is how much users value the sign-in experience.
Okta is built for teams that want clean SSO, dependable MFA, and broad app integrations without forcing users through a maze of one-off credentials. If your goal is to centralize identity and make access decisions based on user, device, and context across cloud and on-prem, this is a strong anchor.
It delivers on core outcomes G2 users care about: friction-light single sign-on that cuts password sprawl; reliable authentication (from OTP and push to phishing-resistant methods) that doesn’t bog down everyday workflows; and deep integrations with a wide ecosystem of SaaS and legacy apps so you’re not building brittle, one-off connectors. In fact, 93% of G2 users rate the authentication experience highly.
Reviewers consistently highlight how quickly users adapt to the Okta dashboard/portal, launching the apps they need without hunting links, and how admins can plug Okta into the rest of the stack (HRIS for automatic onboarding/offboarding, EDR/MDM for device posture, SIEM/ticketing for visibility and handoffs). That ecosystem fit shows up in the feedback as fewer “where do I log in?” tickets and smoother day-two operations.
From an operator lens, G2 reviewers repeatedly call out usability. The setup feels straightforward, policies are understandable, and everyday management doesn’t require deep identity engineering. 94% of G2 users rate its self-service password reset feature highly.
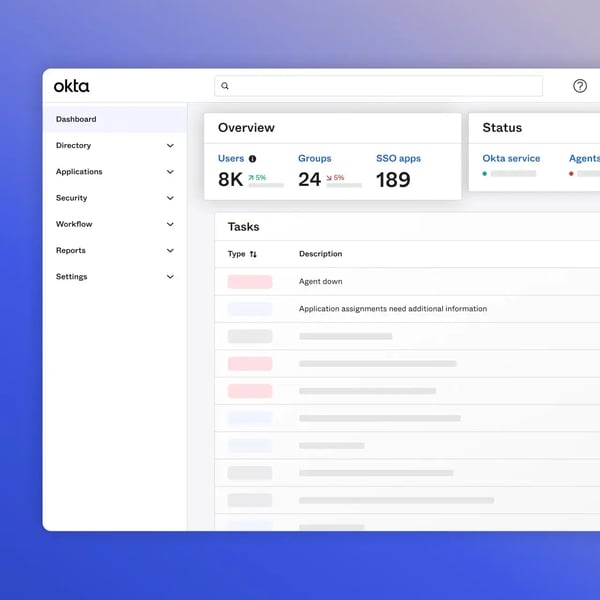
Teams like that app assignment and group-based policies scale cleanly as the org grows, and that availability/performance is solid enough that sign-in fades into the background for most users. When the platform is wired into your existing tools, audits get easier because access paths are centralized and logged.
Security depth beyond SSO. Reviewers frequently highlight Okta’s strong policy engine and adaptive access controls, including context-aware decisions based on device, network, and risk signals, which strengthen zero trust posture without adding complexity.
Extensive integration ecosystem. Multiple reviews praise Okta’s wide connector library and prebuilt app integrations, which reduce custom development work and make it easier to plug identity into the broader security stack.
Users also say that Okta is reliable and highly available. Several users point to consistent uptime and strong performance, noting that authentication remains stable even as traffic scales or during peak usage periods.
Let’s talk about console density. G2 reviewers value the control and breadth, fine-grained policy and broad integrations, while noting the console can feel busy if you’re expecting plug-and-play. That density suits admins who prioritize high-signal telemetry and precise policy design; teams seeking a lightweight, minimalist UI may find it more than they need.
Strong policies and device checks raise assurance on sensitive access, and G2 users note this can surface more prompts than "invisible" setups. That's a win for organizations that favor risk-tight enforcement, and teams that tune MFA frequency and session policies to match their risk model find the prompts settle quickly, delivering the security payoff without sustained friction.
The repeated G2 themes and a strong 4.5/5 rating on G2 point to Okta as a dependable identity core for zero trust: easy SSO, strong MFA, and broad integrations that make secure access feel routine. If you invest a bit of time in console orientation and tune MFA/session policies to match your risk model, you get the payoff most reviewers describe: fewer credentials to manage, clearer access paths, and a cleaner handoff between security and productivity.
“Ease of login and security - the ease of teaching new employees how to use it“
- Okta review, Serena D.
“At times, troubleshooting integration issues or understanding detailed logs can be time-consuming, as the interface for diagnostics is not always very intuitive. Improved reporting and easier debugging tools would enhance the overall admin experience.”
- Okta review, Mahi S.
Find leading Risk-Based Authentication software on G2. Discover adaptive authentication platforms that balance user experience with enterprise-grade security.
The reason FortiClient keeps surfacing in G2 reviews for this category is consolidation. It brings together next-gen antivirus, VPN, web filtering, and ZTNA controls in a single, lightweight agent, replacing the patchwork of disconnected tools many teams rely on. If your goal is to secure endpoints and remote access without deploying a stack of separate products, FortiClient is built to consolidate that footprint.
Reviewers value having everything in one place. The unified approach simplifies compliance and reduces gaps between security layers, and it shows in the numbers: 96% of G2 users rate the platform's ability to meet their requirements, the highest among the five tools on this list.
A theme that came through clearly in reviewer feedback is the tight integration with the broader Fortinet Security Fabric. FortiClient connects seamlessly with FortiGate firewalls, FortiClient EMS for centralized management, and FortiSIEM for threat correlation, and G2 users describe this as a genuine force multiplier. When FortiClient detects a threat on an endpoint, indicators of compromise can be shared automatically across the fabric, triggering quarantine workflows and firewall blocks without manual intervention. For teams already in the Fortinet ecosystem, this native integration translates into faster response times and fewer gaps between detection and enforcement.

Reliable VPN connectivity is the feature G2 reviewers interact with daily, and it's consistently praised. Users describe stable, fast connections for remote access that hold up across network transitions. Reviewers note that once configured, the connection runs quietly in the background and requires minimal intervention, making remote work feel seamless rather than like a constant battle with connectivity tools.
The deployment experience comes up frequently as a positive. FortiClient's agent is small in size and straightforward to push out at scale, and reviewers describe the initial setup as manageable, particularly for teams already using FortiGate, where the installation and configuration for basic VPN and endpoint protection is largely guided. G2 users appreciate that the agent runs without heavy system resource usage during normal operation, keeping endpoint performance smooth for everyday work.
From an operator perspective, G2 reviewers call out FortiClient EMS as a practical strength. The centralized console enables policy management, compliance tracking, and real-time monitoring across all endpoints from a single view. Admins describe being able to push configurations, track security events, and ensure compliance without hopping between tools, and that unified management shows up in feedback as fewer oversight gaps and faster response when something needs attention.
G2 users also highlight the platform's real-time protection capabilities. Behavioral analysis, next-gen antivirus, and host-based firewall work together to catch malware, zero-days, and ransomware. What reviewers find particularly valuable is the automated response: when a threat is detected, FortiClient can share threat intelligence across the Fortinet fabric and trigger containment workflows without waiting for manual escalation. That automation means security teams spend less time chasing alerts and more time on strategic work. The platform holds a 94% rating for both adaptive access control and identity scoring on G2.
FortiClient delivers deep security controls and comprehensive endpoint visibility, but some G2 reviewers note that the management console interface could feel more modern, and VPN error diagnostics can be cryptic when connections fail, particularly for teams less familiar with Fortinet environments. Reviewers who invest time in learning the admin workflows and leverage FortiClient EMS for centralized management report that the platform becomes intuitive, and the depth of control it provides ends up being a competitive advantage over more surface-level tools.
The comprehensive real-time scanning and protection strengthen security posture significantly, though some G2 reviewers note that full scans and updates can temporarily impact performance on older endpoints. Teams that schedule scans during off-hours and manage update rollouts through EMS report that day-to-day performance stays smooth, and the trade-off of deeper protection with scheduled maintenance windows is one most reviewers describe as well worth it for the security gains.
For teams operating within the Fortinet ecosystem, or those looking to consolidate endpoint security, VPN, and zero trust controls into a single agent, the platform delivers practical, measurable value with a deployment model that scales from mid-market to enterprise.
"The unified One Agent approach is excellent. Having EDR, VPN, and web filtering managed through a single lightweight client reduces system bloat and simplifies security compliance across the entire organization."
- FortiClient review, Alejandro A.
"The security vulnerabilities that have often been the cause of data breaches. Perhaps the Fortinet team should look into this aspect to ensure that such incidents do not happen again."
- FortiClient review, Christian N.
Got more questions? G2 has the answers!
For cloud-first access, pair Okta for identity-driven SSO/MFA and conditional access with Zscaler Private Access (ZPA) for user-to-app connectivity without VPNs. Add Cisco Duo as an MFA layer for teams that need fast, push-based identity verification across cloud and on-prem apps.
Lean teams typically get quick wins with Cisco Duo (fast MFA with minimal setup) paired with ZPA (simple, policy-driven access to internal apps). If you also want endpoint protection and VPN in one agent, FortiClient consolidates security controls without requiring a complex multi-vendor stack.
Enterprises often combine Okta (directory/SSO/MFA + lifecycle) with Zscaler Private Access (user-to-app connectivity and global scale). For plants, labs, or smart buildings, Palo Alto Networks IoT/OT Security adds device discovery, risk scoring, and segmentation. FortiClient rounds out endpoint protection for organizations already in the Fortinet ecosystem.
For internal apps, ZPA brokers direct user-to-app access based on identity and device posture. Keep permissions clean in Okta (groups, conditional access), and layer Cisco Duo on top for push-based MFA that adds verification without slowing login workflows.
If "network safety" means cutting lateral movement and stopping unauthorized access, ZPA removes broad network exposure by going app-by-app. Use Okta to centralize authentication so access stays tied to user and device context, and add Cisco Duo for adaptive MFA that verifies identity at every access point.
Startups usually want fast rollout and minimal overhead: Cisco Duo for quick MFA with easy onboarding, plus ZPA to publish internal tools without standing up VPNs. If you're opening offices or need endpoint protection as you scale, FortiClient covers VPN and security in a single agent.
Protect data by aligning identity, access, and endpoints: Okta applies conditional access, ZPA ensures least-privilege paths to sensitive apps, and Cisco Duo adds push-based MFA at every access point. For endpoint protection across devices, FortiClient prevents malware and enforces web filtering alongside secure remote access.
SaaS-heavy teams do well with Okta (centralized SSO/MFA and app governance) plus ZPA (secure access to private build tools, admin panels, and databases). Layer Cisco Duo for adaptive identity verification that strengthens access control without adding friction to developer workflows.
If offices and branches are in scope, pair ZPA for private app access with FortiClient for endpoint protection and VPN connectivity. Use Okta to gate access and Cisco Duo for multi-factor verification. For facilities with connected devices, add Palo Alto Networks IoT/OT Security to discover and segment IoT/OT.
Building durable access control shouldn’t mean wrestling with clunky clients or brittle network tunnels. The five tools I tested make it easier to deliver secure, personalized access, whether you’re focused on retiring VPNs, segmenting sensitive apps, or enabling contractors and BYOD safely.
Each pick is a highly recommended option for reducing the attack surface and stabilizing the user experience. Some shine for fast, lightweight rollouts; others go deeper with analytics and segmentation as you scale. I highlighted what each does well, and where to watch for limits, so you can move faster toward a zero trust posture that actually holds up.
Now it’s your turn: compare your top two or three, map them to your stack and risk areas, and choose the platform that keeps users moving while keeping threats contained.
Ready to layer adaptive challenges on top of ZTNA? Explore the best risk-based authentication software to pair zero trust access with step-up MFA based on user and device risk.
Tanuja Bahirat is a content marketing specialist at G2. She has over three years of work experience in the content marketing space and has previously worked with the ed-tech sector. She specializes in the IT security persona, writing on topics such as DDoS protection, DNS security, and IoT security solutions to provide meaningful information to readers. Outside work, she can be found cafe hopping or watching football. Connect with her on LinkedIn.
Managing access across different apps can get complicated fast. Strong passwords help, but...
 by Washija Kazim
by Washija Kazim
In my years writing about cybersecurity, I’ve learned one universal truth: no one wakes up...
 by Soundarya Jayaraman
by Soundarya Jayaraman
In the pre-single sign-on (SSO) era, I never conveniently browsed an application as I got...
.png) by Shreya Mattoo
by Shreya Mattoo
Managing access across different apps can get complicated fast. Strong passwords help, but...
 by Washija Kazim
by Washija Kazim
In my years writing about cybersecurity, I’ve learned one universal truth: no one wakes up...
 by Soundarya Jayaraman
by Soundarya Jayaraman


