September 15, 2023
 by Soundarya Jayaraman / September 15, 2023
by Soundarya Jayaraman / September 15, 2023
Web applications power our online experience day in and day out. We connect, interact, shop, and watch funny cat videos – all using web apps. They deliver vital business services and hold sensitive data, but the more we use something, the more prone it becomes to assaults.
One cyberattack to watch out for on apps that exploit vulnerabilities in structured query language (SQL) is the common and dangerous SQL injection.
SQL injection (SQLi) is a harmful code injection technique cyber attackers use to exploit vulnerabilities in web applications. They leverage the weak spots to gain unauthorized access by adding a string of malicious code to a database query.
SQL injection attacks lead to improper data access, manipulation, identity theft, financial loss, reputation damage, and legal consequences. Developers and organizations have to understand its risks and implement full security measures. Tools like web application firewalls (WAF) software and digital forensics software are designed to guard against SQL injection attacks. Businesses can also depend on comprehensive website security suites to protect their apps.
Read this SQL injection cheat sheet to know how SQL attacks are executed with examples, their variations, and how to prevent such attacks.
SQL injection has been in the Open Worldwide Application Security Project’s (OWASP) top 10 list of web application security risks for years. In 2022 alone, OWASP found 274,000+ occurrences of some form of injection in the apps they tested; SQL injection and cross-site scripting (XSS) were the most common.
Attackers can use SQl injections to cause:
These destructive actions irrevocably damage businesses. The offenses compromise privacy and data integrity, leading to a loss of customer trust and business reputation. It also adds a financial burden to the company dealing with the aftermath.
It’s been more than two decades since SQL injection first came on the scene. Twenty years later, it remains notorious, as evidenced by the following prominent SQL injection incidents.
Let’s look at the basics of databases and SQL queries we use in modern web applications. This will help us understand the inner workings of SQL injection better.
All websites use relational databases, also called SQL databases, to store data about their users and apps. It could be user info, login credentials, payment information, or anything else about the company. Take an e-commerce website, for instance. It stores product data, user accounts, order data, and payment information in its database.
The websites then take the data from these databases and deliver content or services specific to the users. This process happens thanks to SQL, a standardized programming language used for managing databases. Whenever you need to get something from an app, say your purchase history, you’re, in fact, making a request to the database using SQL queries, a command that instructs a database to perform a specific action.
In an attempt to make web interactions seamless, many websites let users enter data to make SQL queries. This can include things like search terms, usernames, or payment details.
Consider the e-commerce website’s example. A simple SQL query to display your order history from the database with "orders" table (o) and a "products" table (p) will be as follows:
SELECT o.order_id, o.order_date, p.product_name, p.price
FROM orders o
JOIN products p ON o.product_id = p.product_id
WHERE o.user_id = 12345;
This SQL code picks the order ID and date from the orders table, along with the product name and price from the product table for USER ID 12345 from the website database. Typically, the ID will be based on input from the user. Problems arise when the input isn’t properly checked and controlled. Attackers exploit this vulnerability to carry out an SQL injection attack.
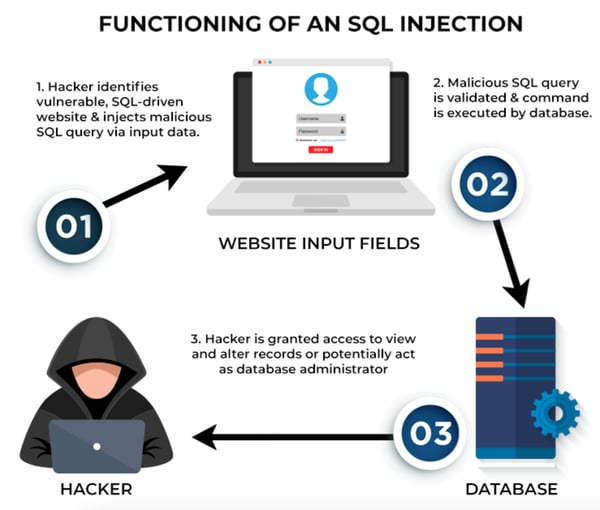
Here's how it typically unfolds.
Consider a web application that uses a URL parameter to fetch product details based on a product ID, like this:
http://example.com/products?id=1
An attacker might try to inject malicious SQL code to cause an error and retrieve information like this: http://example.com/products?id=1' OR 1=1; –
If the application fails to validate and sanitize user input adequately, the SQL query could be manipulated as follows:
SELECT * FROM products WHERE id = '1' OR 1=1; - - ';
In this case, the original query was designed to retrieve a product with ID 1, but the attacker's input modifies the query to return all products because of the addition of 1=1 and the appended double hyphen (- -). It nullifies the original closing single quote and leads to consequences displaying all product details or revealing error messages that attackers can exploit.
of web application critical vulnerabilities in 2022 were due to SQL injections.
Source: Statista
The widespread prevalence of SQL vulnerabilities and the attraction of the web app database with all its business-critical data makes SQL injection one of the most persistent cyberattacks.
 Source: Spiceworks
Source: Spiceworks
There are three major types of SQL injection attacks based on how attackers retrieve information or interact with the database:
In-band is the most common type of SQL injection attack. The classic hacker uses the same communication channel (in-band) to inject malicious SQL code and retrieve the results. The two main variations of in-band SQLi are:
This attack leverages the UNION SQL operator, used to combine data from the result of two or more SELECT statements. By doing this, attackers can retrieve data from tables they don't have direct access to.
In this technique, an attacker intentionally triggers errors in an SQL query to exploit the error messages returned by the database. The errors can reveal valuable information about the database structure, table names, column names, and sometimes the data itself. Error-based SQLi can also be executed as out-of-the-band SQLi.
In a blind SQLi, the attacker cannot directly see the results of their assault. Instead, they infer information by observing application behavior or error messages that respond to their queries. This type of attack is time-intensive as hackers have to make a series of SQL queries to find potential vulnerabilities to exploit. Two variations of blind SQLi are:
Here, the attackers ask queries that make the database delay its response before it reacts. They infer information about the database by paying attention to response time.
For Boolean blind SQLi, attackers take advantage of the way an application responds to true or false conditions in SQL queries. Based on the web application’s responses, they infer information about the database, even though no data from the database is returned.
An out-of-the-band SQLi attack causes the application to send data to a remote endpoint controlled by the hackers. An attack like this requires the SQL servers to have certain features, like being able to initiate external network requests like Hypertext Transfer Protocol (HTTP) requests.
Preventing SQL injection requires a multi-layered approach involving secure coding practice and continuous monitoring. Here's a cheat sheet with essential steps to help keep you safe from SQL injection attacks.
The primary defense against SQL injection attacks is prepared statements with parameterized queries. Prepared statements ensure user inputs are treated as data rather than executable code.
Developers compile SQL codes for queries in advance as templates with placeholders for input values from the user. At the query execution time, the prepared statements bind actual values instead of placeholders. This stops malicious code execution.
Prepared statements are favored over dynamic SQL statements. They write SQL queries during the execution time, which weakens them against injection attacks.
Here are language-specific recommendations for using prepared statements (parameterized queries) in popular database programming:
Another SQL injection prevention method is the use of stored procedures or a group of pre-compiled SQL codes that can be used again and again.
Input validation involves checking user input to make sure it meets specific criteria before processing. An allow-list, also known as a white list, is a key aspect of input validation. Here, only predefined, safe values or patterns are accepted as part of SQL queries. Any input that doesn't match the set criteria is rejected. This actively prevents malignant or unexpected input from entering the system.
Object-relational mapping (ORM) libraries are valuable tools for developers working with relational databases. They let developers interact with databases using the programming language of their choice, and thereby reducing the need for writing raw SQL queries. ORM libraries provide built-in protection against SQL injection attacks.
Train the developers and IT teams on secure coding practices. Make sure to do regular security audits and penetration testing to find vulnerabilities.
Tip: Help your programmers and developers learn secure coding faster with secure code training tools.
The least privilege principle only gives database users the minimum permission required to do their jobs. Following this principle reduces the impact of potential SQL injection attacks, or any cyberattack, for that matter. Also, apply strict access control to your database.
A WAF monitors incoming network traffic of applications and blocks potential malicious traffic based on a list of well-known attack signatures.
* Above are the five leading WAF solutions from G2’s Summer 2023 Grid® Report.
A WAF employs predefined rules to detect suspicious patterns and anomalies in incoming traffic, like SQL keywords and malicious payloads. It sanitizes and validates user inputs and blocks or filters out harmful requests. This helps stop dangerous SQL queries as they enter the system.
Modern WAFs adapt to new attack methods using machine learning.
In addition to WAF, several other security platforms impede SQL injection attacks.
SQL injection attacks pose a grave threat to web app security. Companies risk losing valuable data, user privacy, and their good reputations if the attacks succeed.
While no single solution guarantees absolute safety against SQL injection, combining the preventive measures we talked about here significantly reduces the chance of attacks. Web developers and database administrators should employ stringent defenses and fortify their web apps against potential exploitation.
Want a comprehensive solution to secure your website? Explore web security software and how it helps against cyber attacks that leads to data breaches.
Soundarya Jayaraman is a Senior SEO Content Specialist at G2, bringing 4 years of B2B SaaS expertise to help buyers make informed software decisions. Specializing in AI technologies and enterprise software solutions, her work includes hands-on testing of tools, comprehensive product reviews, competitive analyses, and industry trends that empower buyers to choose solutions with confidence. Outside of work, you'll find her painting or reading.
Keeping your database in good shape helps manage scaled systems and run operations without...
 by Holly Landis
by Holly Landis
As large language models (LLMs) become embedded in enterprise applications, from virtual...
 by Washija Kazim
by Washija Kazim
Modern mobile marketing, powered by mobile advertising software, has changed how businesses...
 by Jagmeet Singh
by Jagmeet Singh
Keeping your database in good shape helps manage scaled systems and run operations without...
 by Holly Landis
by Holly Landis
As large language models (LLMs) become embedded in enterprise applications, from virtual...
 by Washija Kazim
by Washija Kazim


