The internet can be a scary place.
Because of this, we often turn toward a Virtual Private Network, otherwise known as a VPN, to provide a safe, secure, and fast connection to all of what the world wide web brings to our fingertips.
When choosing a VPN provider, we often make note of which VPN protocols they have to offer, which can set one VPN apart from the other. But what exactly is a VPN protocol?
What is a VPN protocol?
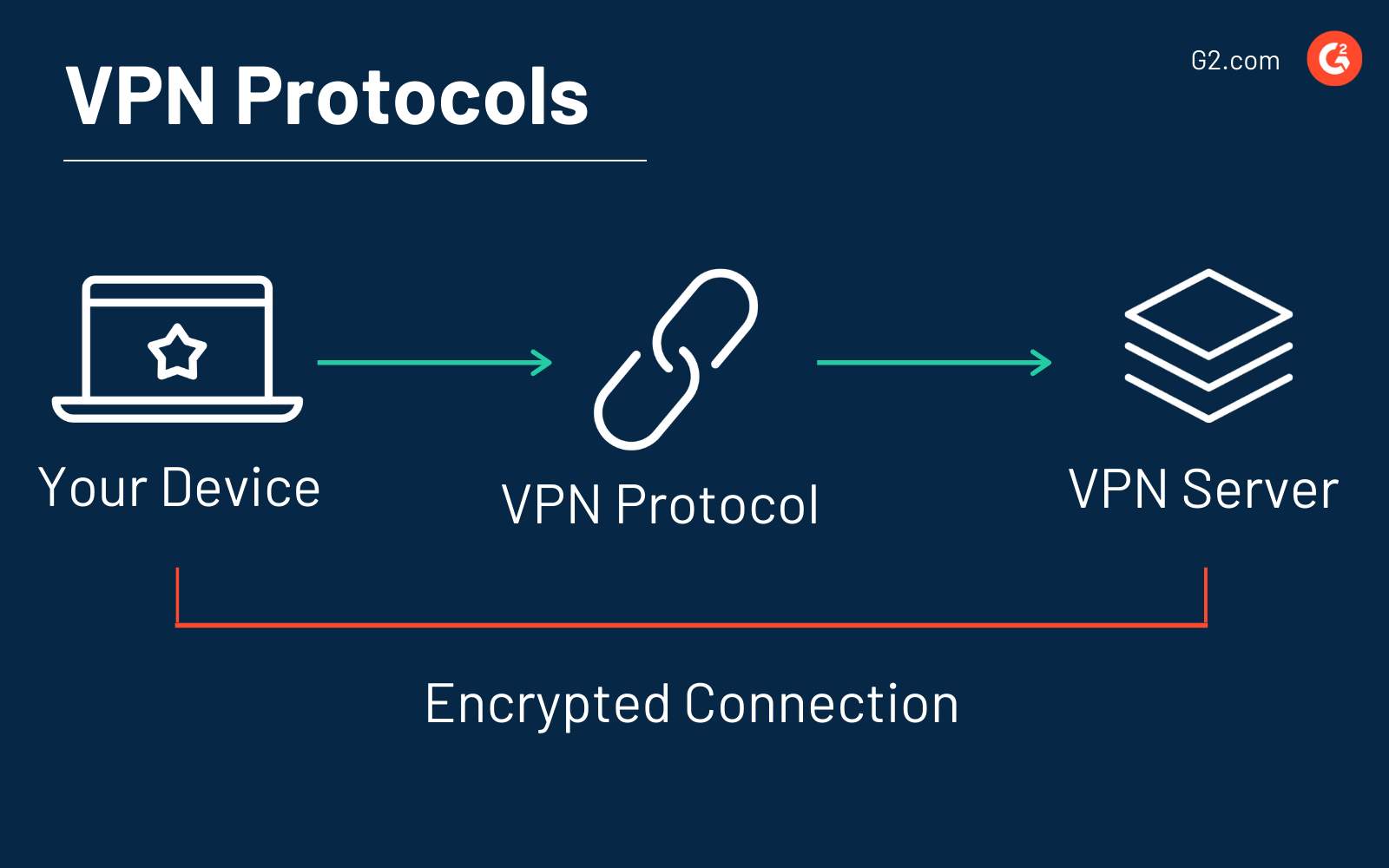
A VPN protocol is a set of rules or instructions that will determine how your data routes between your computer (or other device) and the VPN server. VPN providers rely on protocols to ensure a stable and secure connection.
Protocols have unique specifications that offer benefits to the VPN user based on the circumstance. Some may specialize in privacy while others put an emphasis on speed. VPNs utilize different protocols depending on the device being used, what you want to do, and how you want to do it.
For instance, if you’re at home watching Netflix, it won’t do you any harm to select a VPN protocol with fewer security measures to speed up your internet connection. This way, you can spend more time engrossed in your favorite TV show rather than waiting for it to load.
The opposite applies when you’re doing things online that present a risk to your data, like shopping and banking on an unsecured network.
As you research your options when it comes to VPN software, most will tell you about the VPN protocols they support. To fully understand what this means and how this may impact how you browse the web, it’s best to know the ins and outs of the various types of VPN protocols.
Types of VPN protocols
The protocol within the VPN is the technology used that offers different encryption standards for the transmission of data. When you have an active connection to a VPN, the protocol leads the data between your device, the server, and back again.
The most popular VPN providers are the ones that have the most protocols for their users to access, which is why these providers invest their time and energy to include the best protocols on the market.
Below are the most widely used VPN protocols on the market.
1. PPTP
One of the first VPN protocols to become available was PPTP, which stands for Point to Point Tunneling Protocol.
The main draw toward using PPTP is that it can be set up easily on every major operating system. It was developed in the mid-1990s by Microsoft with the purpose of being integrated with Windows 95 since it was specifically designed for dial-up connections. The predominant use of PPTP was for connecting to the internet and the intranet.
As technology has become much more advanced, the basic encryption methods used in PPTP began to be easily thwarted by hackers, which compromises its security. Thanks to low encryption standards, this type of VPN is extremely fast, but not very secure.
|
Pros |
Cons |
|
Integrated into several operating systems |
Extremely lacking in security |
|
One of the fastest VPN protocols |
Can be blocked by firewalls |
|
Easy to set up |
Monitored by the NSA |
|
Great for streaming content that is geo-restricted |
Anonymity may be compromised |
2. L2TP/IPSec
This type of VPN stands for Layer 2 Tunneling Protocol over Internet Protocol Security. It’s more secure than PPTP and offers more features to its users.
It’s comprised of two parts:
- L2TP for the secure connection
- IPSec for the encryption of data
Alone, L2TP doesn’t provide any encryption or privacy until it is paired with the security protocol IPSec. Because of the parts within this protocol, it can be slower than PPTP because that traffic is converted into L2TP form, followed by the extra layer of encryption for security.
It was developed in the 1990s by Cisco and Microsoft and is commonly used for accessing the internet through a VPN when the top concerns are security and privacy. It’s also relatively easy to set up since the support for this protocol has been pre-built into most modern computers as well as our mobile devices.
|
Pros |
Cons |
|
IPSec encrypts your data to military standards, while L2TP runs on mobile operating systems |
The encryption can take up a lot of computing power, causing a slow connection |
|
Prevents data from being altered between the sender and the receiver |
Can be difficult to configure |
3. OpenVPN
OpenVPN is one of the most popular VPN protocols on the market and is used by the majority of VPN providers in the world.
Developed by James Yonan and released in 2001, it’s open-source and published under a GNU Public License. This means that it provides the community access to the source code so that any security flaws can be easily identified and dealt with, instead of allowing potential flaws and backdoors to exist within the code.
Offering up a blend of both speed and security, OpenVPN is available on many different platforms, such as Windows, Mac, Android, iOS. It’s commonly used for third-party VPN clients since it isn’t built into computers or mobile devices. It comes in handy for users who want to bypass online restrictions since it’s hard to be detected by firewalls.
OpenVPN has two main types:
- OpenVPN TCP
- OpenVPN UDP
OpenVPN TCP is the most common and the most used on the internet. It’s based on the Transmission Control Protocol. When combined with the Internet Protocol, they create a specific set of rules for how computers exchange information back and forth. It’s considered to be extremely reliable, especially when the utmost in security is needed.
Open UDP, which stands for User Datagram Protocol, is targeted toward a low-latency transmission of data. This means that it doesn’t put as much emphasis on security and is best used for things like gaming, video streaming, and audio streaming.
It is often referred to as the “gold standard” of VPN protocols thanks to its reliability.
|
Pros |
Cons |
|
Uses modern security measures to keep data secure |
Can be difficult to configure |
|
Can bypass firewalls since it’s easily disguised as normal internet traffic |
If configured incorrectly, security will be compromised |
4. SSTP
SSTP stands for Secure Socket Tunneling Protocol and was developed by Microsoft and first built into Windows Vista. While it can work on Linux, despite it being somewhat challenging, it’s mainly thought of as a VPN protocol that is specific to Windows technology.
SSTP was built to be used for remote access, which means it has a tendency to struggle with site-to-site VPN access. Because it comes built-in, SSTP is primarily used by those who favor Windows as their operating system.
|
Pros |
Cons |
|
Extremely secure and can get around firewalls |
Isn’t supported on other operating systems, like Mac |
|
Easy to use since it’s completely integrated into Windows technology |
Software isn’t open-source, meaning it hasn’t been independently audited |
5. IKEv2
IKEv2 stands for Internet Key Exchange volume 2, which was developed by Microsoft and Cisco and is paired with IPSec for encryption and authentication. Its main use is for mobile devices, either on 3G or 4G LTE, since it’s good at reconnecting whenever a connection is dropped.
A dropped connection typically occurs when a user drives through a tunnel and temporarily loses surface, or when they switch from the mobile connection to WiFi.
This means that when you switch from a WiFi connection to a data plan connection on your smartphone, or move between hotspots, the VPN connection will remain stable throughout the process without any drops.
|
Pros |
Cons |
|
Relatively fast, stable, and safe |
Isn’t widely supported, unless you use a Blackberry |
|
Handles network changes without issues |
Can be difficult to implement on the VPN server-side |
6. Wireguard
Wireguard is a relatively new open-source VPN protocol that is still considered a work in progress.
It runs on Linux and is said to have better performances than both OpenVPN and IPSec. While still being developed, it’s already available for several platforms. Because it’s so new, it’s not yet commonly found in a consumer VPN app.
One of the draws of Wireguard is that it’s extremely fast. The reason? This VPN protocol has 4,000 lines of code, while others have tens of thousands of lines. Less code also means less space for error.
|
Pros |
Cons |
|
Easy to set up |
Still in development |
|
Offers tech advantages, like faster connection times and enhanced reliability |
Waiting on which apps will support it |
7. SoftEther
What started as a project at the University of Tsukuba in Japan, SoftEther ended up growing into a massive open-source, multi-protocol VPN software project.
The thing to remember about SoftEther is that it can either refer to the VPN protocol or the VPN server.
- The protocol: Uses SSL for secure VPN client-server communications with various technological improvements that make it fast and secure.
- The server: Can support a large number of VPN protocols, like SSTP, OpenVPN, IPSec, and the SoftEther protocol.
Even though it’s fairly new, SoftEther is quickly growing in popularity. It also works across multiple operating systems and is one of the few VPN protocols that boasts working clients on Linux.
|
Pros |
Cons |
|
Secure, stable, and fast |
No native OS support |
|
Free to use |
Will need to be installed on a device and connected to the server |
Want to learn more about Business VPN Software? Explore Business VPN products.
Frequently asked questions about VPN protocols
Users of VPNs usually have specific questions when it comes to protocols. Below, you’ll find the most common questions, plus the answer.
Which VPN protocol is the fastest?
When you’re looking for speed, and speed alone, choose PPTP. Especially if your main use will be streaming geo-blocked content. Just remember the lack of encryption will leave you relatively exposed online.
If you want speed and security, choose SoftEther or IKEv2.
Which VPN protocol is the most secure?
If the utmost in security is what you’re looking for, go with OpenVPN. SoftEther would be a good choice, too. It all depends if you’re looking to use something newer to the world of protocols, or one tried and true like OpenVPN.
Which VPN protocol is best for torrenting?
If you’re interested in using a VPN protocol for torrenting, which is a file-sharing protocol based on peer-to-peer technology, you’ll need one that’s fast, stable, and secure. For all of these features, go with SoftEther.
Your second-best option? IKEv2.
Disclaimer: We at G2 do not support or encourage illegal copyright infringement or illegal torrenting. However, we do understand that some VPN users are interested in file-sharing, especially as a way to access entertainment, work, or school files.
Which VPN protocol is the most stable?
When it comes to stability, especially when bouncing from network to network on a mobile device, go with IKEv2.
SoftEther is another good choice since it runs constantly once it’s set up and its code was written to prevent crashes.
Which VPN protocol is the easiest to set up?
Because PPTP is built into so many platforms, it’s the easiest VPN protocol to set up. The same can be said for L2TP/IPSec and IKEv2. If you’re a fan of Windows products, SSTP is your best bet.
SoftEther is relatively simple, too, since it comes with an easy-to-use installer.
Which VPN protocol is compatible with the most platforms?
Because PPTP is available across multiple operating systems and devices, it’s the most natively supported VPN protocol.
However, it’s important to note that, because of its lack of security measures, it might not be supported on new devices and operating systems. So, it’s going to depend on which device you’re using. For example, if you have macOS Sierra (released September 2016), or anything newer, PPTP isn’t supported.
Other options if you have newer software include L2TP/IPSec and IKEv2.
Which VPN protocol should I use?
Unfortunately, there isn’t a black and white answer to this question. It’s going to depend on what you want to do when browsing the internet. Here’s a quick breakdown of what each protocol is best used for:
- PPTP: Fast access to geo-blocked content. Just remember not to log in to any account that contains sensitive information.
- L2TP/IPSec: Downloading torrents, accessing geo-blocked content, browsing the internet safely… as long as you don’t mind a potential dip in connection speeds.
- OpenVPN: Secure and stable internet connection.
- SSTP: Best for Windows users that are looking for online security and speed.
- IKEv2: For browsing on a mobile device or when you want to secure your online traffic and enjoy a decently fast connection.
- Wireguard: Best for Linux users or those interested in a smooth online experience.
- SoftEther: A newer protocol that is a great alternative to OpenVPN, as it also boasts a fast and secure connection.
Life is full of choices
When choosing a VPN provider, take special note of the VPN protocols that are within its list of features. While it may suit your needs to choose a provider that offers a low-security protocol, like PPTP, chances are you’ll need something that offers more security.
Of course, there’s no right or wrong choice of protocol, just make sure you pick a provider with protocols that meet all of your expectations.
When you know which VPN protocol you prefer, and have picked a provider that suits you, learn how to set up a VPN and start browsing the web safely.

Mara Calvello
Mara Calvello is a Content and Communications Manager at G2. She received her Bachelor of Arts degree from Elmhurst College (now Elmhurst University). Mara writes customer marketing content, while also focusing on social media and communications for G2. She previously wrote content to support our G2 Tea newsletter, as well as categories on artificial intelligence, natural language understanding (NLU), AI code generation, synthetic data, and more. In her spare time, she's out exploring with her rescue dog Zeke or enjoying a good book.
